Use the ssh-keygen command to generate a public/private authentication key pair. Authentication keys allow a user to connect to a remote system without supplying a password. Keys must be generated for each user separately. If you generate key pairs as the root user, only the root can use the keys.
- But I can not find the genkey file in my system by find / -name genkey.So I generated the key pair by myself,use the ssh-keygen command: ssh-keygen -t rsa -b 2048 -N ‘’ -C “cpesn” -f genkey -q The key pair was copied into /etc/ssh. After this,I modifed the sshcallhome.xml, pasted the private key and public key into hostkeyconfig.xml.
- Create an open key for SSH/SFTP communication. Usable characters are ASCII 0x20-0x7e (32 bytes) other than '0'. The default key length is 1024, and the character string is blank. If you do not specify this parameter, an open key with the default value will be created.
- Ssh-keygen is able to generate a key using one of three different digital signature algorithms. With the help of the ssh-keygen tool, a user can create passphrase keys for any of these key types. To provide for unattended operation, the passphrase can be left empty, albeit at increased risk.
- Ssh-keygen -q -t rsa -N ' -f /.ssh/idrsa &1 /dev/null Or, under a bash like shell, If you certainly want to overwrite the previous one, use just a here-string to feed the command with all the need input: ssh-keygen -q -t rsa -N ' &1 /dev/null From ssh-keygen man page:-N newpassphrase provides the new passphrase.
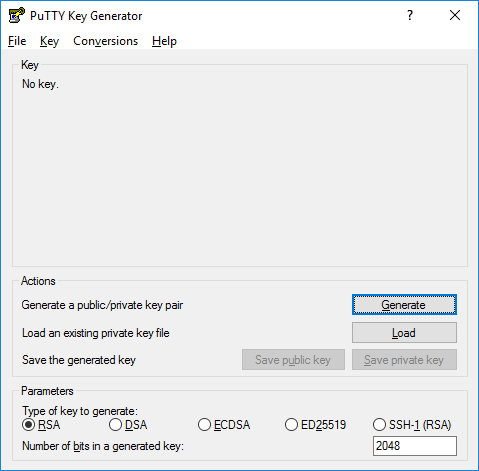
The following example creates the public and private parts of an RSA key:
DESCRIPTION top ssh-keygen generates, manages and converts authentication keys for ssh (1). Ssh-keygen can create keys for use by SSH protocol version 2. The type of key to be generated is specified with the -t option.
Use the –t option to specify the type of key to create. Possible values are “rsa1” for protocol version 1, and “dsa“, “ecdsa“, or “rsa” for protocol version 2.
You have the option of specifying a passphrase to encrypt the private part of the key. If you encrypt your personal key, you must supply the passphrase each time you use the key. This prevents an attacker, who has access to your private key and can impersonate you and access all the computers you have access to, from being able to do so. The attacker still needs to supply the passphrase.
The ssh-key command in the example generated two keys in the ~/.ssh directory:
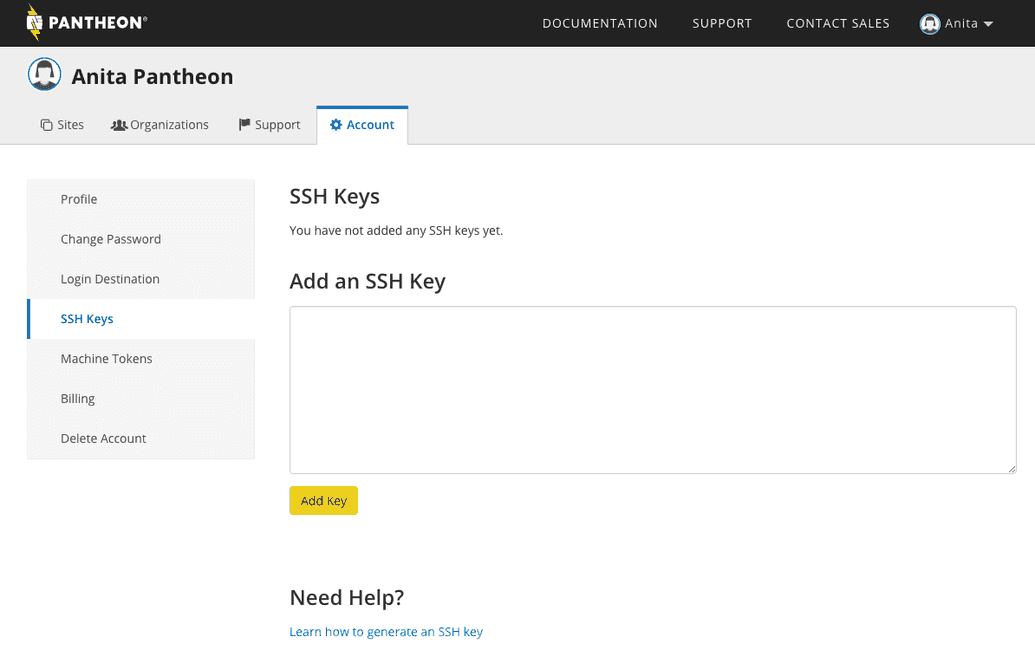
To log on to, or copy files to, a remote system without supplying a password, copy the public key (~/.ssh/id_rsa.pub in this example) to ~/.ssh/authorized_keys on the remote system. Set the remote ~/.ssh directory permissions to 700. You can then use the ssh or scp tools to access the remote system without supplying a password.
To allow multiple connections, append the public key to the authorized_keys file on the remote system instead of copying it. The following example appends the public key:
You can improve system security even further by disabling the standard password authentication, and enforcing the key-based authentication. To do so, set the PasswordAuthentication option to no in the /etc/ssh/sshd_config configuration file as follows:
This disallows users whose keys are not in the authorized_keys file of the specific user on the server to connect via ssh. The connection is denied and the following message appears:
Setting the PasswordAuthentication option to yes, which is the default, permits a user to use a password for authentication.
Use the 'ssh' command to view and configure SSH settings.
View settings
Data compression communication settings
msh> ssh compression {on|off}
The default is 'on'.

SSH/SFTP communication port setting
SSH/SFTP communication timeout setting
msh> ssh timeout [0-65535]
The default is 300.
SSH/SFTP communication login timeout setting
msh> ssh logintimeout [0-65535]
The default is 300.
Github Ssh Genkey
Setting an open key for SSH/SFTP
msh> ssh genkey {512|768|1024} 'character string'
Create an open key for SSH/SFTP communication.
Usable characters are ASCII 0x20-0x7e (32 bytes) other than '0'.
The default key length is 1024, and the character string is blank.
If you do not specify this parameter, an open key with the default value will be created.
Deleting open key for ssh/sftp communication

Ssh Keys Windows
If you do not specify a character string, current setting is displayed.
ssh can be used only with sftp.
